Validate AWS CIS security benchmarks with prowler
Despite the number of Amazon Web Services that have the word simple in their titles, keeping on top of a large cloud deployment isn’t an easy ask. There are a lot of important, complex, aspects to consider so it’s advisable to pay attention to the best practices, reference architectures, and benchmarks published by AWS and their partners. In this post we’ll take a look at the CIS security benchmark and a tool that will save you a lot of manual verifying.
CIS, the “Center For Internet Security”, publish best practice, security configuration guides, that present a number of recommendations that you should be aware of if you’re running production workloads in AWS. You don’t have to change your environment to suit every recommendation, or even agree with them, but you should read through it once and note where you’re consciously different to their advice. The guide itself, which you can find on the CIS AWS Benchmark page, or as an AWS static whitepaper link that doesn’t require an email address to read, is quite low level but well worth a read. Being aware of all the potential issues will help shape your cloud environments for the better. But, as good, lazy, admins we won’t go and check each of the recommendations by hand. Instead we’ll use an application called Prowler.
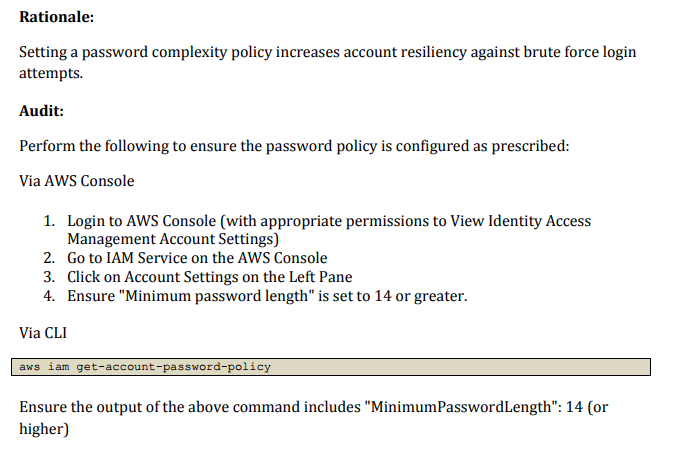
The recommendations are terse but mostly clear. As the screenshot shows they aid in verification and remediation by presenting instructions for how to reach the given values in the web console or via the CLI.
Prowler however provides us a third way. It has checks for most of the recommendations, and even some bonus extras, and will iterate through them and assign us a pass or fail for each. Let’s install it and run some experiments.
Installing prowler
Prowler is written in shell but uses a few python libraries so we’ll
install it, and the required dependencies, into a virtualenv to keep
the versions isolated.
# create a new virtual env
virtualenv prowler-sweep
cd prowler-sweep
source bin/activate
# Get prowler from github
git clone https://github.com/toniblyx/prowler
cd prowler
# install the dependencies
pip install ansi2html awscliYou now have all the code required for prowler to run a sweep of your
security settings.
Running prowler
I uses different profiles, configured in .aws/credential for most of my
experiments so for now I’ll run prowler as me, but with read only access. If
you want to run this as a dedicated user or under EC2 the installation guide has
lists the required IAM permissions.
./prowler -p full-readonly
_ __ _ __ _____ _| | ___ _ __
| '_ \| '__/ _ \ \ /\ / / |/ _ \ '__|
| |_) | | | (_) \ V V /| | __/ |
| .__/|_| \___/ \_/\_/ |_|\___|_|v2.0-beta2
|_| the handy cloud security tool
Date: Wed 30 May 18:47:25 BST 2018
In its most basic mode prowler will run from the command line and show its
results in glorious, colourful, ANSI.
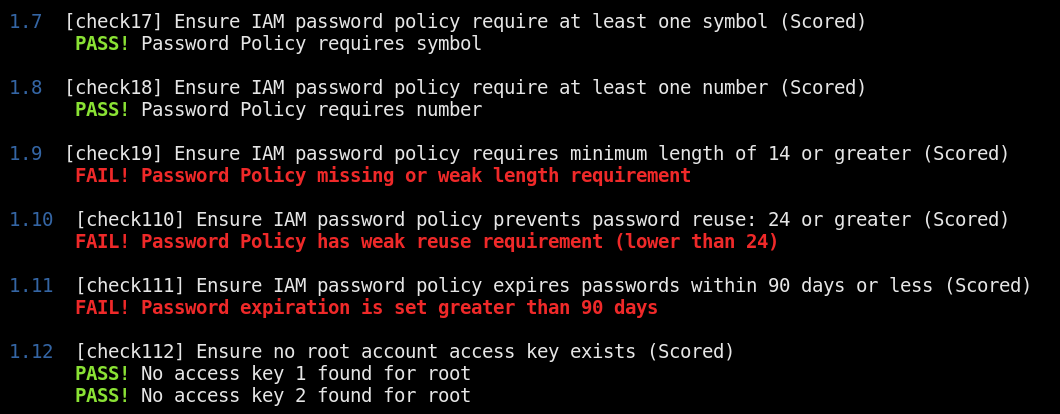
In additional to text with control characters it can also provide basic HTML reports or even JSON and CSV for further processing and integration into your existing tools. Once you’ve finished a full sweep in your format of choice you can start to prioritise the findings and often add remediation to your Terraform or CloudFormation code bases.
Above and beyond
In addition to the CIS recommendations Prowler adds some of its own checks, for example some services didn’t exist when the last benchmark was published, and for common operational practises that are worth following. You can even extend it yourself if you have local rules or compliance requirements. There’s a list of additional prowler checks and description on the GitHub repository.
AWS security is a big, sprawling, topic with many moving parts, and while no third party resource will ever cover all your use cases documents like the CIS benchmark and tools like prowler can help quickly provide a baseline and safety net to ensure if you do get breached it won’t be because of a simple oversight.